Heavy Scans for Low-Hanging Fruit
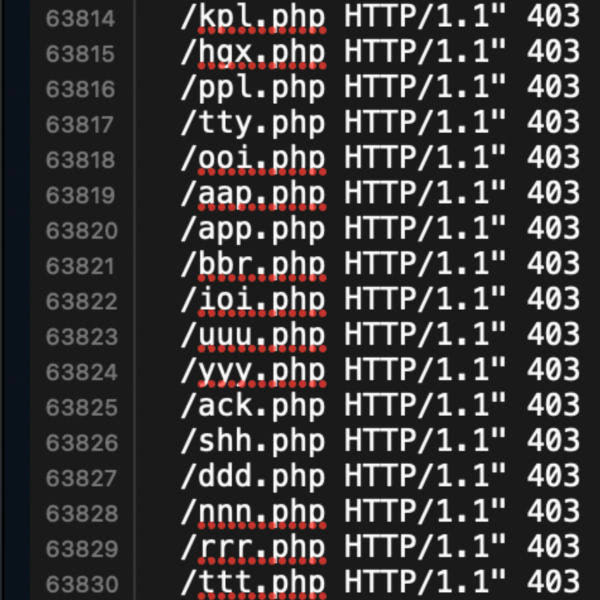 I’ve been working on developing the 8G Firewall. Digging through log files and crunching the data, the big new trend I’m noticing is heavy scanning for easy targets, low hanging fruit. Bad actors are looking for any little hidden files stashed on your server. Mostly PHP files, also ZIP and RAR files, and other file formats commonly used for compressing and archiving content.
I’ve been working on developing the 8G Firewall. Digging through log files and crunching the data, the big new trend I’m noticing is heavy scanning for easy targets, low hanging fruit. Bad actors are looking for any little hidden files stashed on your server. Mostly PHP files, also ZIP and RAR files, and other file formats commonly used for compressing and archiving content.
Basically, anything that might contain useful information (like login credentials, database backups, email addresses, etc.). Also, 99% of the requests for these files target the public root directory. Noticing a high volume of requests for such files across servers. Just malicious little bots searching for anything you (or anyone) might have forgotten about.
99% of the requests for these files target the public root directory.
Some Examples
To get a better idea of what I’m referring to when I say “low hanging fruit”, let’s look at some examples of the types of files being targeted. There are many such files, with names usually ranging in length between one and four characters. For single-digit names, they basically scan for all of them:
0.php
1.php
2.php
3.php
.
.
.
a.php
b.php
c.php
.
.
.
x.php
y.php
z.phpBut they’re not stopping with single-character names. Here are some examples of targeted file names containing two characters. They’re not looking for every letter combination, just certain ones. Like things they imagine people would name their one-off, odd little experiments and temporary files, for example:
0z.php
db.php
xx.php
fx.php
up.php
go.php
me.php
ok.php
hi.php
v1.php
v2.php
1a.php
2c.php
3uv.php
45.php
it.phpSo they’re digging around in the cracks, looking for loose or otherwise forgotten files stashed in the corners of servers around the Web, low-hanging fruit like:
bak.php
web.php
x0x.php
you.php
404.php
777.php
100.php
www.php
new.php
doc.phpBecause you just know that there are people out there who actually name their files things like www.php and new.php. And most likely such files contain some sort of information that can be exploited somehow. That’s obviously what the scanners are thinking, and just based on the sheer volume of these types of scans, apparently the strategy is paying off for them (or they wouldn’t be doing it).
More examples
Most scans or probes or whatever you want to call them are looking specifically for PHP files. But also seeing heavy activity searching for file formats like TAR, RAR, ZIP, GZ, like tar.gz and other compressed formats, for example:
www.rar
www.zip
wwwroot.rar
backup.zip
wpzip.php
bak.7z
web.rarAlso commonly requested, files named with short words and common phrases. Software names and abbreviations, etc. For example, info.php is a very popular file name, as are files with names such as these:
blog.php
test.php
note.php
hide.php
info.php
vuln.php
1984.php
2020.php
wp.php
ws.php
wii.php
cms.php
wp2.phpAgain, these are file names that people might use when moving stuff around on the server, saving data, making backups on the fly, etc. A good example is the humble index.php file. They’re relentlessly looking for variations on index.php, like:
1ndex.php
1index.php
123index.php
xindex.php
sindex.php
index1.php
index2.php
index3.php
.
.
.Do people actually name index files things like index1.php and then leave them on the server? Sadly, YES. It’s an easy way to make a quick backup or snapshot of a file or script. And those are the types of loose, rogue files that are heavily targeted.
Backup files
Beyond simple one-off file names such as those discussed above, the “low fruit” scans also are searching for backup files. Scanning for backup files is nothing new, just noticing a LOT more of it these days. Here are some examples of the types of keywords and file names they’re looking for:
wordpress1
old1
old2
OLDSITE
beta
staging
BKP
old-site
123
oldwebsite
blog
dev
newsite
home
BACKUP
old_files
Old
demo
site
wordpress-old
backup
oldsitehere
BAK
oldsiteback
devnewThere are hundreds if not thousands of variations on the above keywords. When used in file scanning, the above keywords may be used in file names or directory names. For examples:
# File names
/archive.zip
/backup.sql.gz
/old_files.rar
/wp-config.php.old
/db_backup.tar
# Directory names
/wordpress1/
/wordpress-old/
/staging/
/newsite/
/backup/In either case — file names or folder names — the requests are 99% aimed at the public root directory of your site. You know, where the home page is located. Gotta keep that directory (all directories, but especially that one) squeaky clean at all times.
Further discussion
As mentioned, I’m working the next version of the nG Firewall, which blocks a LOT of these “low-hanging fruit” type requests. Such requests are tricky to block because you never know which files are legit. The targeted file names all comprise common characters like letters and numbers. 8G Firewall strives to balance effective blocking of short file names with a minimal rate of false positives.
Of course, bad bots and spammers are scanning for anything they can find, not just files with short names. That is why I develop firewalls like 7G, 8G, and BBQ/Pro. These firewalls offer strong protection against a wide range of threats and malicious requests. They work well with very low number of false positives, because they aren’t blocking requests for anything that could be a legitimate file.
The downside to minimizing false positives is that many requests for small random file names make it through. But really, if the file doesn’t exist, the only difference between blocking and allowing is the response code, either 403 “Forbidden” or 404 “Not Found”, respectively. In some cases however, for example with WordPress, returning a 404 response typically means loading up PHP, the database, assets, and everything else. Whereas returning a 403 response typically requires only a few bytes of data. Thus, blocking as many short-filename requests as possible can help to improve your site’s performance.
All that in mind, best advice to avoid getting stung by one of these scans is to just make sure that your server is clean of any one-off odd whatever files. Just stick with the core app files and related assets, etc. Any files that are not part of the project, and not used for anything, should be removed from the server. If you need to store something on the server, lock it down with authentication or just deny all public access via private directory or similar.
Closing thoughts
Take-home message for admins and developers is to avoid using short, simple file names. Instead follow best practice and use descriptive naming for all files, especially if they’re located in the public root directory of your site. For example project-name-date-version.php is going to be much harder to find than script1.php or some other lazy/weak file name. Using precise, descriptive file names improves the footprint and clarity of your app, while helping to avoid any nefarious entanglements with shady characters and their relentless low-hanging fruit scans.

